Fluxion: The Modern Tool for Auditing Security and Social Engineering Research
Fluxion is a tool for auditing security and researching social engineering. It is a modernization of mindset, which has been obsolete for the last 6 years. Fluxion has numerous features that weren’t available before. This script can obtain the WPA/WPA2 key from a target access point through a social engineering attack. It is fully compatible with our Kali Linux system.
The labor of Fluxion was remarkable.
1. Search for a specified wireless network.
2. Run the Handshake Snooper assault.
3. Obtain a handshake (vital for verification of the password).
4. Launch a Captive Portal attack.
5. Construct a counterfeit (artificial) AP, mirroring the initial access point.
6. Generate a DNS server, rerouting all queries to the aggressor’s host running the captive portal.
7. Generate a web server, giving the captive portal which requests clients for their WPA/WPA2 code.
8. Set up a jammer, detaching all clients from the original AP and enticing them to the counterfeit AP.
9. Every authentication effort at the captive portal is inspected against the handshake file captured previously.
10. The attack will be automatically completed as soon as an appropriate key is given.
11. The key will be logged and customers will be able to reconnect to the desired access point.
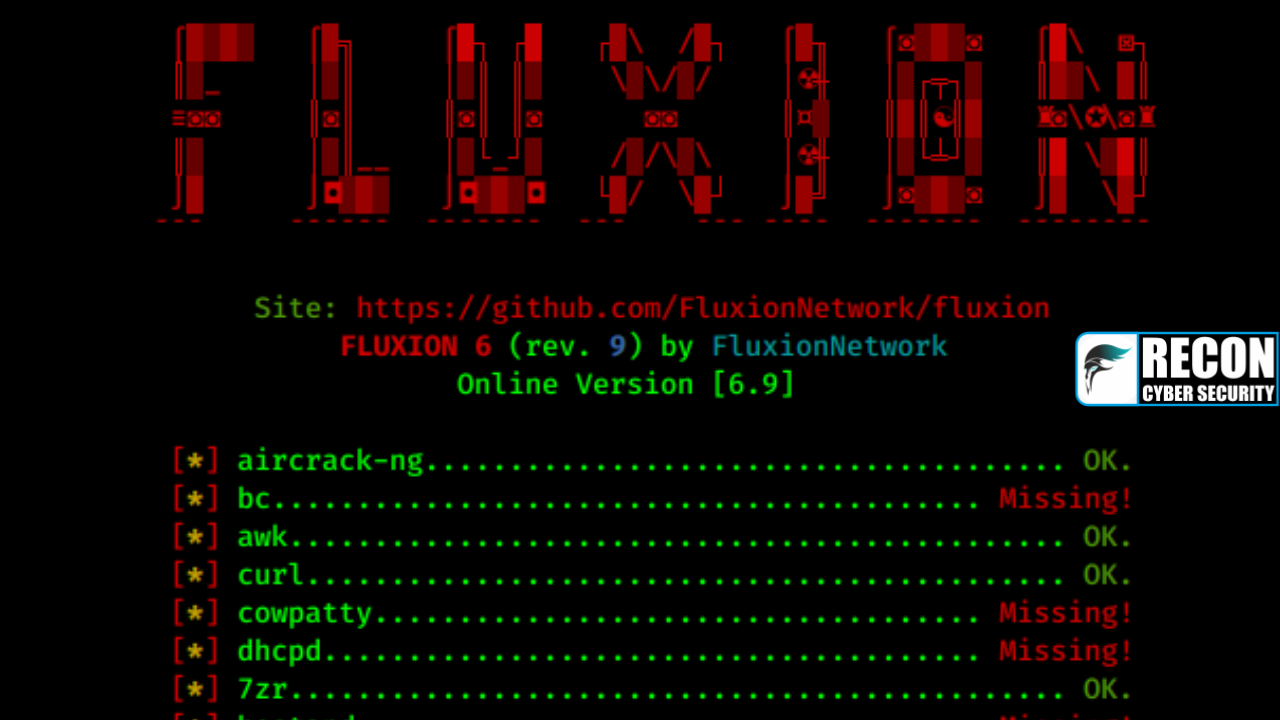
Installation
The installation process of fluxion on Kali Linux is straightforward. Just like other tools, we can clone fluxion from its GitHub repository using the command in the Kali Linux terminal

We can utilize this instruction to duplicate the fluxion onto our device.

We can quickly access fluxion by entering a basic ‘cd’ command.

To initiate the usage of fluxion, we execute the fluxion.sh script, using the -I flag, which installs the essential components.

Starting from now, the -I flag is no longer necessary and simply running the command is enough.

The screenshot below illustrates the installation of missing packages.

After the requirements are met, the program will initiate on its own and request a language to be selected.

To proceed, we must select a wireless interface. Our laptop’s wireless chipset cannot use packet injection and monitor mode, so an external Alfa wireless adapter (AWUS036NEH) is needed, as it is the only one in the market that offers both functions. This can be purchased from Amazon.

To proceed, we should investigate the available Wi-Fi networks in the vicinity.

By entering a dual-band or single-channel frequency, we can begin to explore wireless networks in the vicinity.

When it comes to choosing a wireless interface for tracking, we have the option to go ahead with our selection, or if we are uncertain, to opt for option 3 instead.

After that, it is necessary to decide upon the means of procuring the handshake.

To conduct jamming and monitoring, we must choose an interface, such as our Alfa card, wlan1.

To ensure accuracy, fluxion has recommended a verification hash process which we must now proceed with.

All of the options discussed are simply the fundamentals, and there is nothing else to add. Fluxion will take all of the targets connected to our targeted wireless network and de-authenticate them. Whenever these de-authenticated devices try to reconnect, Fluxion will capture the handshake.

Although we can accomplish the same feat with Aircrack-ng, Fluxion is more advanced and user-friendly. It is also able to perform an Evil-Twin attack, in which continuous de-authentication packets are sent to the target, causing all clients to disconnect. When this happens, we create a duplicate WiFi network with the same name, trapping clients into thinking it is the original, and thus capturing their credentials. It is quite similar to phishing.

THANK YOU!





1 comment